Web applications are getting popular with an increase in digital adoption. Every sector is now taking advantage of web apps as they provide services over the internet and are easily accessible to the customer through web browsers. But as they are increasingly used, they bring security challenges against cyberattacks on financial and personal data.
In the modern business world, security is a top priority. Data breaches are increasing which results in reputational damage to businesses. It reveals sensitive corporate information like client personal information and financial transactions. The only idea that acts as a protection shield to ensure the applications follow security guidelines and are secure is to incorporate web application security practices throughout application development.
It has become crucial nowadays to implement security measures in your web app. Also, ensure you approach custom mobile app development services that integrate robust security practices into your product. This blog informs you about the latest best practices companies have used to safeguard their information.
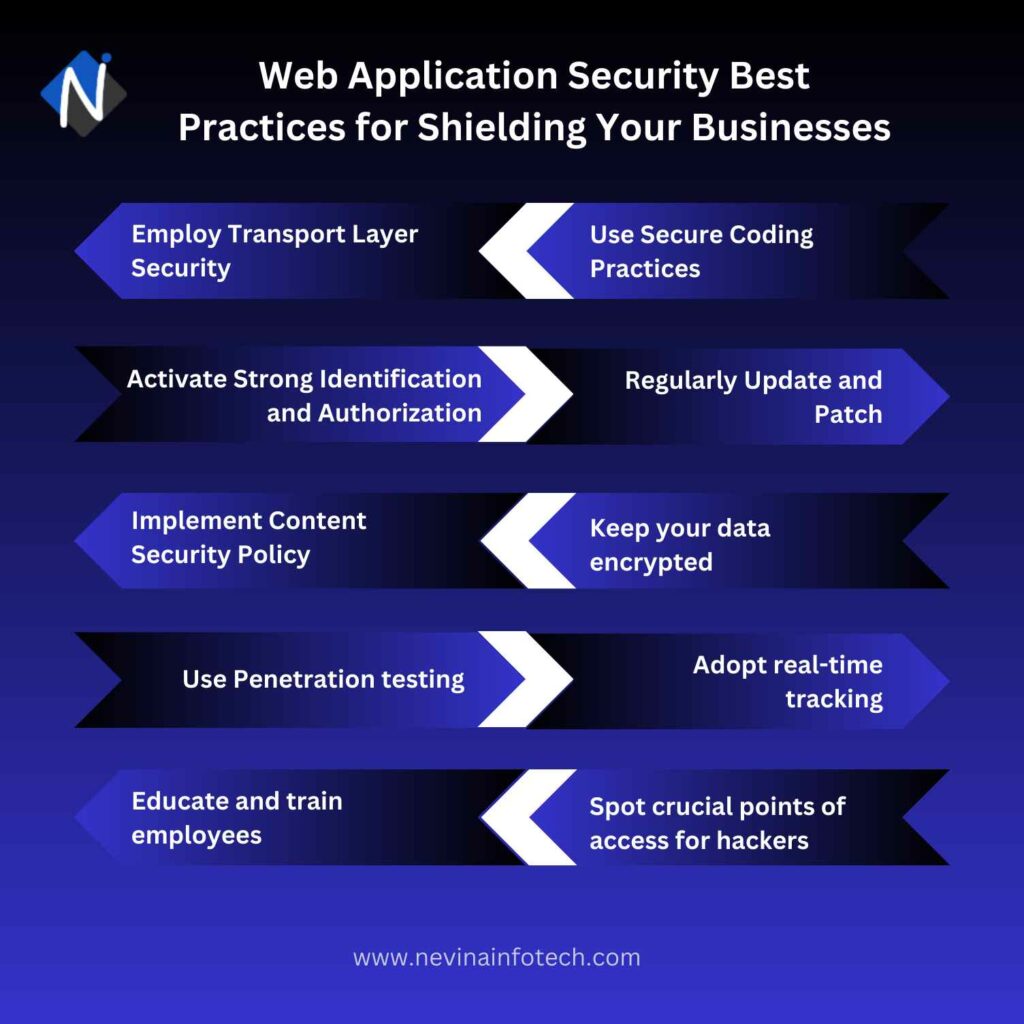
Web Application Security Best Practices for Shielding Your Businesses
Employ Transport Layer Security (TLS):
Implement Transport Layer Security (TLS), or HTTPS, to encrypt communications between your web application and users. TLS secures data transmission to keep sensitive information private and secure from surveillance and manipulation. Establish robust SSL/TLS regulations, safe encryption rooms, and legitimate SSL certificates for your web server from reputable certified authorities.
TLS encryption can assist in defending web applications from attacks and data leaks. Websites should always use HTTPS which is TLS secured. Other browsers follow the Google Chrome browser’s consistent attack on non-HTTPS websites.
Use Secure Coding Practices:
Secure coding practices are the root of building a robust and secure web application. Implement input validation to sanitize and validate user input, preventing common attacks like cross-site scripting (XSS) and SQL injection.
Output encoding is essential to properly encode user-generated content to prevent XSS attacks when rendering dynamic content. Robust error handling is also crucial to avoid exposing sensitive information and providing potential insights to attackers about the application’s infrastructure.
Activate Strong Identification and Authorization:
Focus on creating strong authentication and authorization systems to protect the safety of your web application. Create rigid password policies and advise users to select strong passwords and to change them frequently. Multi-factor authentication (MFA) can be used which adds an additional layer of security by asking users for more detailed verification.
Another crucial element is role-based access control (RBAC), which enables you to give users specific roles and permissions depending on their roles and duties, making sure only authorized people can view sensitive information and functions.
Regularly Update and Patch:
The key to preserving web application security is to keep your app and related software up to date. Keep an eye out for security updates from reliable sources and join appropriate mailing lists. The danger of manipulation is reduced and identified flaws are addressed with the help of regular updates.
Ensure you run the most recent, secure versions by frequently updating your web application, frameworks, libraries, and plugins. Know when software manufacturers release security advisories and fixes. An attacker may be free to exploit known flaws in outdated software.
Web App Ideas For Startups To Make Money
Implement Content Security Policy (CSP:
Content Security Policy (CSP) helps to identify and counter assaults like Cross-site Scripting (XSS) and data injection attacks. These assaults are used for a variety of purposes, including virus delivery, site damage, and data theft. A web page’s Content Security Policy HTTP header must be added and values should be specified what resources the user agent is permitted to load for that page. This is known as configuring Content Security Policy.
Avoid making your policy too restrictive because doing so might cause your online applications to stop working correctly. Create an inclusive approach initially, then slowly add restrictions and test them as you proceed. Maintaining your CSP is necessary to prevent security risks as your application develops.
Keep your data encrypted:
Enable encryption for every user data you send to the server and get back from it. Although man-in-the-middle attacks are virtually complex with HTTPS, it is still insufficient if someone has access to your server. It doesn’t matter who it is; it may be a system administrator or an ex-employee. You require encryption and hashing to protect your data even if someone else has access to it.
When a user submits information through their browser like when logging in or filling out a form it is first encrypted and sent over a secure link to your server, new attack descriptions should be updated continuously. You must check that the web application development services you are approaching must use security solutions that offer strong encryption.
Use Penetration testing:
The most common aspect of any security assessment is penetration testing. For finding weaknesses in your web application’s infrastructure, architecture, and code, perform regular penetration testing. your software is nearly kept in a real scenario where penetration testers mimic actual attacks to find vulnerabilities that attackers could use.
QA engineers try to damage the system using this technique like physical harm or coding to test whether the web application security is working properly or not. you may effectively improve the security status of your application by following this practice.
Adopt real-time tracking:
It can be quite challenging to keep track of your app’s security, especially as it expands. Multiple data streams must be carefully monitored and analyzed to look for any illegal activities or issues. Modern technology has made real-time security monitoring possible. Software that gathers, analyzes & interprets data from various sources can be developed with the help of robust web development services and talented developers.
Set up a dependable monitoring system to track and examine your web application’s logs, traffic, and security events in real-time. Keep an eye out for unusual behavior, security breaches, or suspicious actions. To reduce the effects of assaults and avoid data breaches, quick notice and actions to be taken immediately are essential.
Educate and train employees:
It is already known to us that humans make mistakes. But when they are not aware of what mistakes they can actually make, they won’t be able to resolve them. Maintaining a secure environment is possible only by educating your workforce about web application security. It is really important to make employees aware of their mistakes by organizing security awareness training courses.
It will inform employees about the dangers of web applications, standard attack methods and the best ways to spot and report unusual activities. Emphasize the need for employees to be aware of phishing attacks, and how to identify them also how crucial it is to prevent clicking on fraudulent links or exposing critical information.
Spot crucial points of access for hackers:
It is necessary to identify and categorize possible access points that hackers might use. Analyze the design, APIs, user inputs and third-party integrations of your web application in detail. Understanding your possible weaknesses can help you strengthen those areas and reduce risks by putting in place specific security solutions.
Due to the interaction with customers and transaction processes some components of your program are more prone to security threats than others. Divide your software’s features into modules based on security priorities to ensure that you concentrate on doing web application security testing in the proper manner.
Make Use of Cookies:
The use of cookies is also a very common practice that many firms overlook when discussing best practices for web application security. Both organizations and individuals find cookies to be highly useful. They allow visitors to be remembered by the websites they visit, making subsequent visits quicker and, in several instances, more customized.
Hackers can also manipulate cookies to breach safety and get into restricted areas.
All you have to do is take a step back and look change the settings for your cookies to reduce the risk of attacks.
Conclusion
The increase in cyberattacks has made it really crucial to adopt security measures in web applications as these apps are over the internet the data branches and vulnerabilities are pretty often. You can strengthen the security of your application only by implementing these web application security best practices into your app. Protecting sensitive information and reducing the risk of attacks will protect your business and gain users’ trust.
Awareness about the practices and having top-notch web development solutions that can assist you in creating a unique software solution and achieving significant success in the market is all you need. Nevina Infotech is a well-known web application development services provider with years of experience in serving clients with quality products and affordable costs.
Frequently Asked Questions
What are the major purposes of security attacks on web applications?
The main objectives of security attacks on web applications are getting unauthorized access to sensitive information, benefitting from security flaws, and interfering with corporate operations. It also adds viruses or harmful code to affect user privacy and confidence.
What are the common security breaches on web applications?
The common and dangerous attacks on web application security are:
Cross-site scripting (XXS)
Insecure direct object references
Remote code execution
Failure to restrict URL access
SQL injection etc
How can we defend against hacker attacks on the web application?
Before starting the development process, a web application’s security should be addressed. The best security techniques, including data encryption and multifactor authentication, should be put into place as part of a thoroughly planned web app security strategy. You must perform continuous security checks throughout the development process and keep performing security tests even after your web app goes online. You can add reputable third-party services in your web application, and be sure to keep them updated to the most recent versions as third-party providers frequently release updated versions that address security flaws to the general public.



